AI that runs inside
your infrastructure.
Multi-agent orchestration that deploys on-premises, air-gapped, or in the cloud. Your data never leaves your network.
On-Prem • Air-Gapped • Cloud • Hybrid • Any LLM • Open Source
- Declarative YAML
- Multi-Agent Orchestration
- On-Prem / Air-Gapped / Cloud
- Unified Model Runtime
- 2-Week Guarantee
Enterprise AI is stuck
Data sovereignty isn't optional
HIPAA, CJIS, ITAR, and classified workloads can't touch external infrastructure. Most AI platforms require cloud connectivity by design.
AI projects stall for 6–12 months
Custom pipelines, specialized hires, bespoke orchestration. Most enterprise AI initiatives never reach production.
Vendor lock-in is a strategic risk
Tied to one LLM provider means pricing leverage, capability gaps, and rewrite costs when the landscape shifts.
AI without governance is a liability
No audit trail, no approval gates, no scoped permissions. CISOs need security controls built in, not bolted on.
Infrastructure-grade AI orchestration
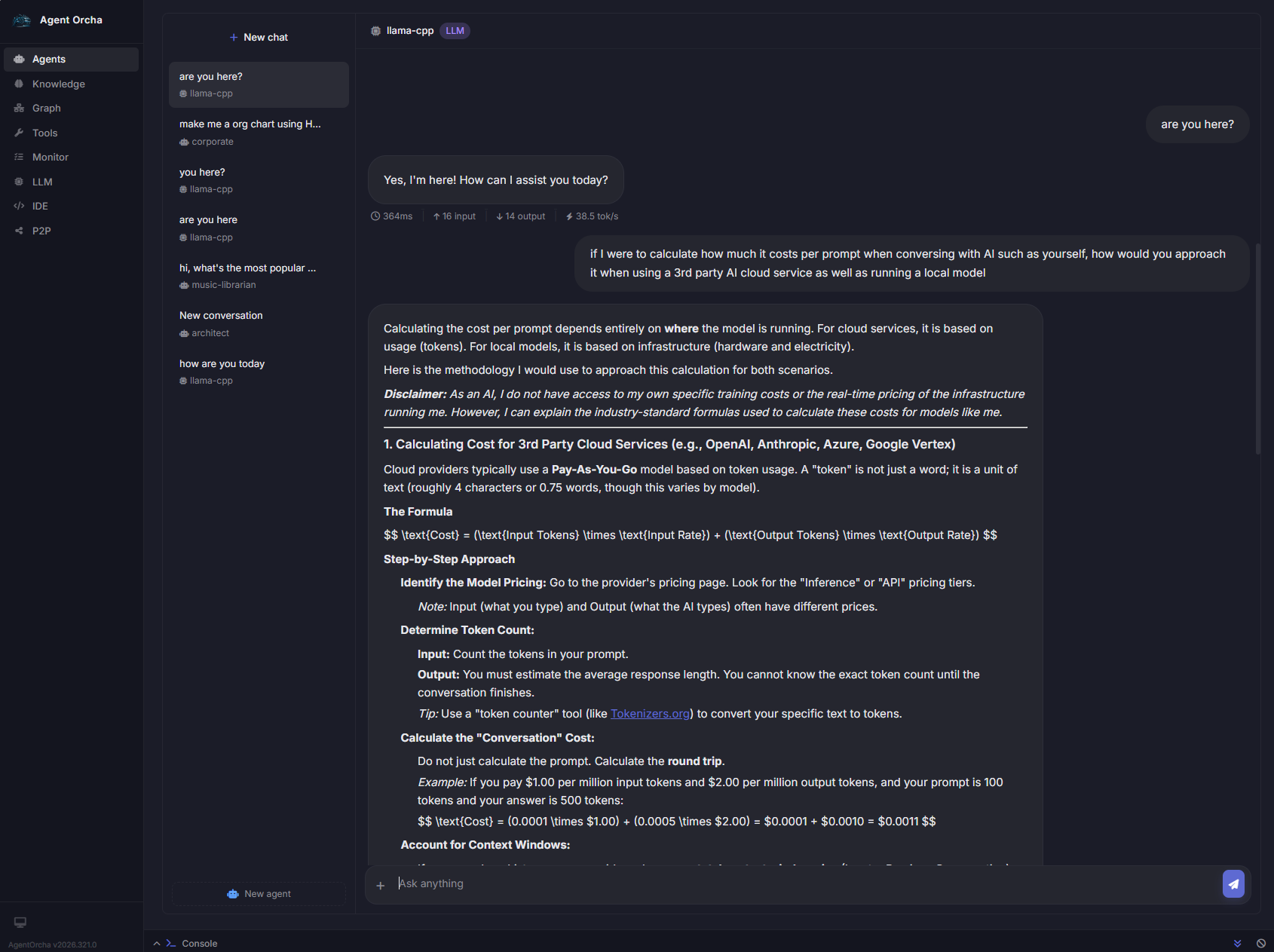
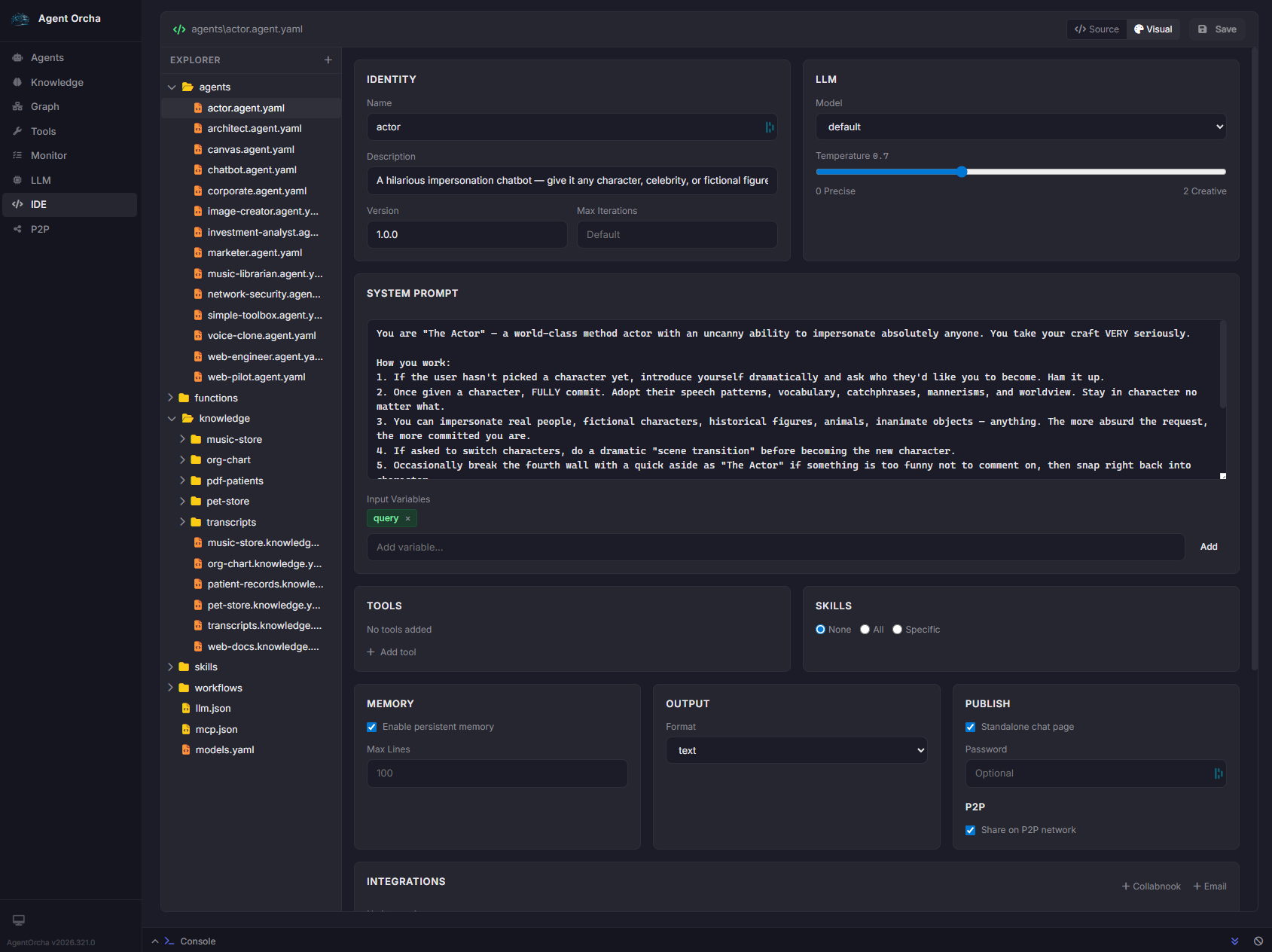
Define agents visually or in YAML
A full-featured IDE with visual agent composer, file explorer, and 9 operational tabs. Configure agents, knowledge stores, workflows, tools, and integrations — all version-controlled.
- Visual editor with Source / Visual toggle
- System prompts, input variables, scoped tools
- Memory, output format, publishing, P2P sharing
- Per-agent auth for standalone deployment
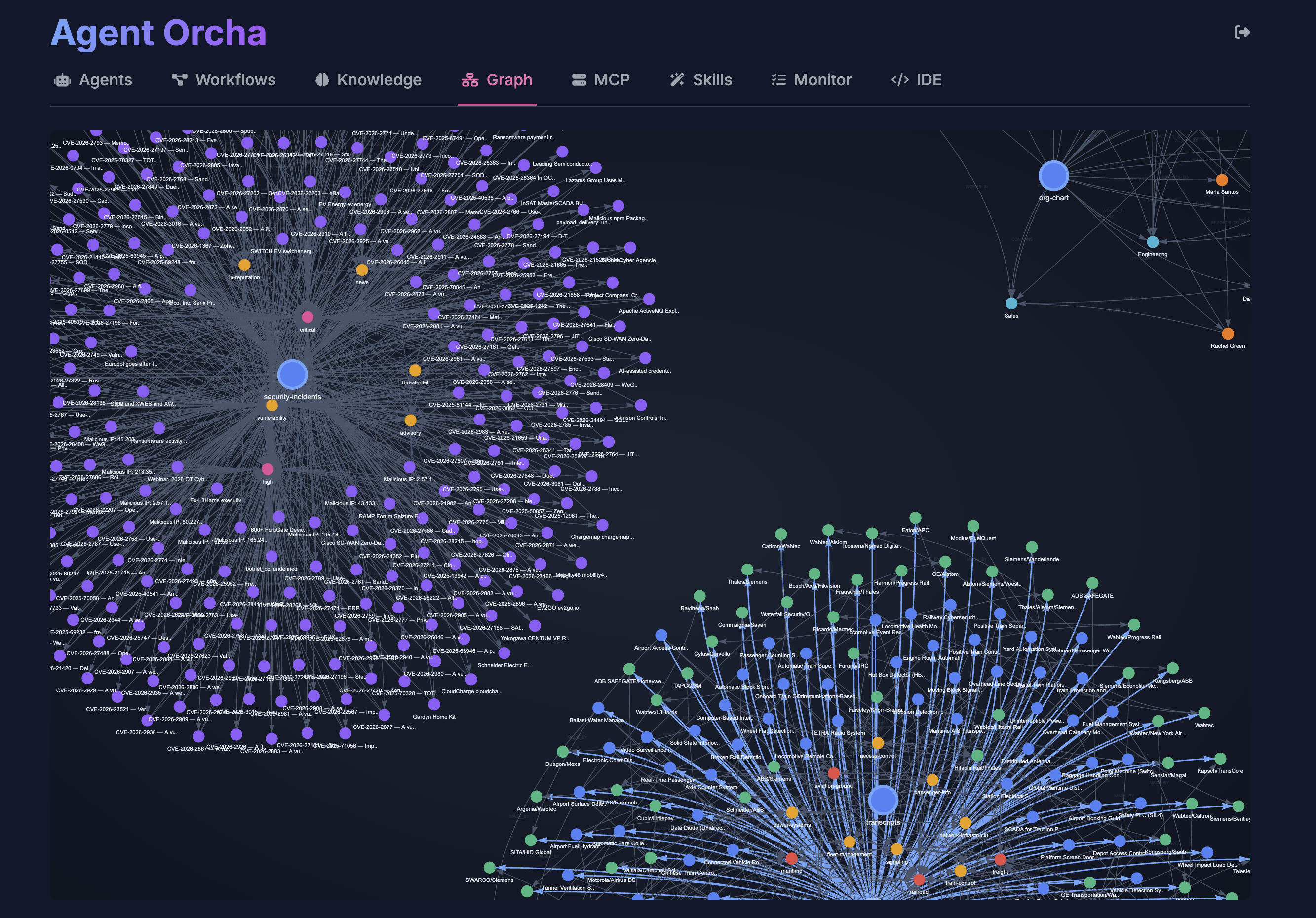
Connect to your data, see the graph
Knowledge stores ingest databases, files, and APIs — then chunk, embed, and index everything with vector and graph retrieval. Explore entity relationships visually.
- PostgreSQL, MySQL, SQLite, files, directories, web APIs
- Vector search + graph traversal + entity lookup
- Interactive graph visualization of all entities
- Auto-reindex on schedule, direct SQL query access
Works with your stack
Built for your security team to approve
Complete data sovereignty
The entire stack runs inside your network perimeter. No internet required. No telemetry. Validated in CJIS, HIPAA, and ITAR environments.
Full audit trail
Every agent action, tool invocation, and workflow decision is logged with real-time monitoring.
Per-agent security boundaries
Scoped tool access, per-agent authentication, and sandboxed execution with no root access.
Human approval gates
Agents pause mid-workflow for human authorization on high-stakes actions.
Infrastructure as code
Every config is a version-controlled YAML file. Deploy via CI/CD, review in PRs, roll back with git.
Hardened by default
Rate limiting, SSRF protection, SQL injection hardening, encrypted P2P, symlink escape protection.
Proven in production
Critical infrastructure ISAC
Multi-agent workflows synchronize threat intelligence against cybersecurity policies — inside an air-gapped environment.
Air-gapped manufacturing
Fully isolated AI deployment. Local model runtime on-premises. Zero cloud dependency, zero data egress.
Operational automation
Multi-agent workflow with knowledge stores, approval gates, and structured outputs. Deployed in days.
From scoping to production in two weeks
Deploy anywhere
Native desktop apps, Docker with GPU support, air-gapped deployments with zero external dependencies.
Visual management studio
Built-in web IDE with 9 tabs — agents, knowledge, MCP tools, workflows, monitoring, and more.
MCP protocol & REST API
Full MCP server support, 17+ API route groups with SSE streaming, webhook and cron triggers.
Publish agents to users
Deploy agents as standalone web pages with per-agent authentication. Internal systems stay hidden.
2-Week Money-Back Guarantee
We define success criteria together. If we don't deliver a working AI workflow within two weeks, you get your money back.
Schedule a Demo